In February 2017, Microsoft announced the general availability of Blob Auditing for Azure SQL Database. While auditing features were available before in Azure, this is a huge leap forward, especially in having more granular control over what audit records are captured.
Before Blob Auditing, there was Table Auditing. This is something I like to equate to the C2 auditing feature of SQL Server. It’s only configurable options were ON or OFF. In reality, Table Auditing has a few more controls than that, but you get the idea. There was no way to audit actions against one specific table. Blob Auditing provides us with that level of granularity. However, controlling that granularity cannot be accomplished through the Azure Portal; it can only be done with PowerShell or REST API.
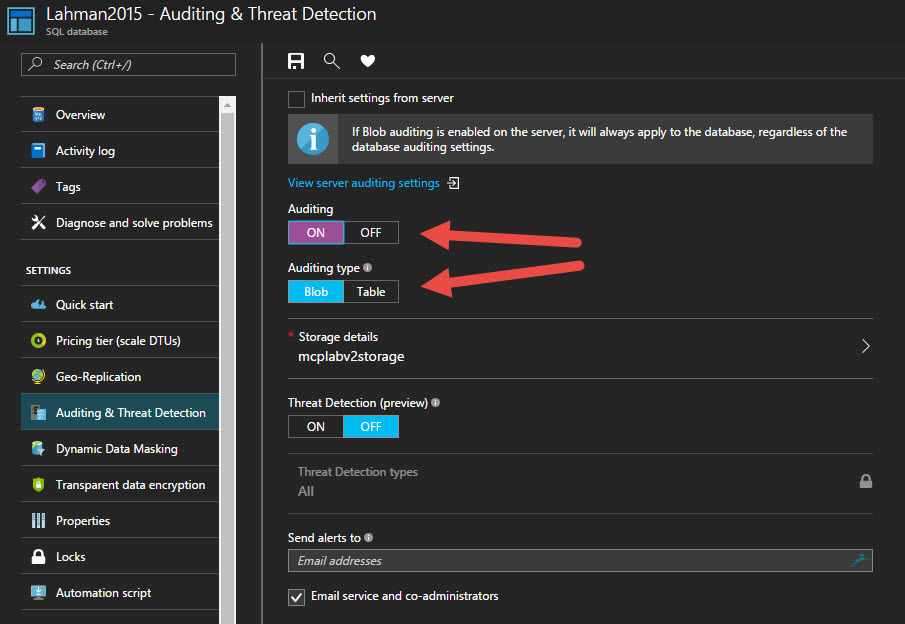
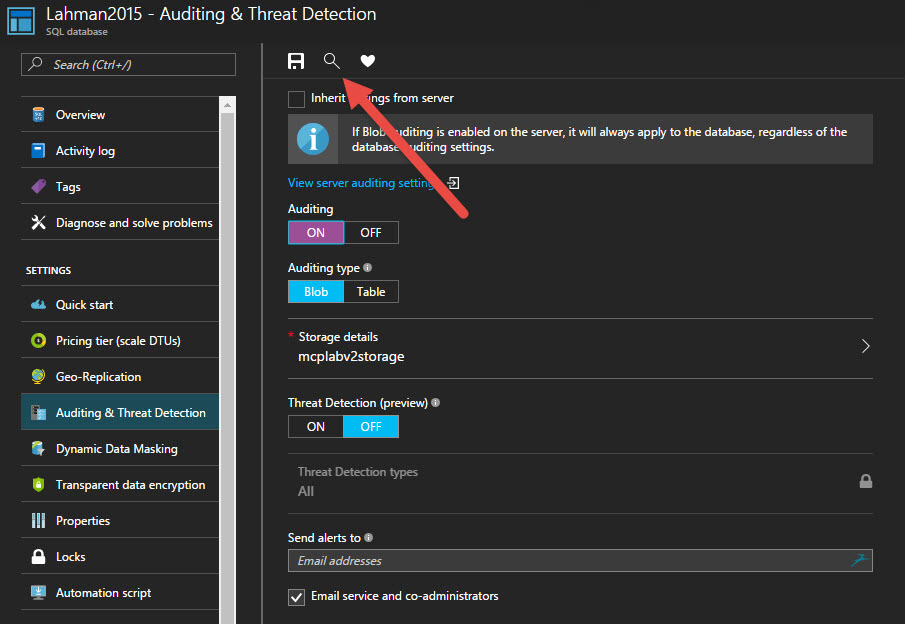
In the image below, you can see that Blob Auditing is on, but we can not see what actions are being collected.
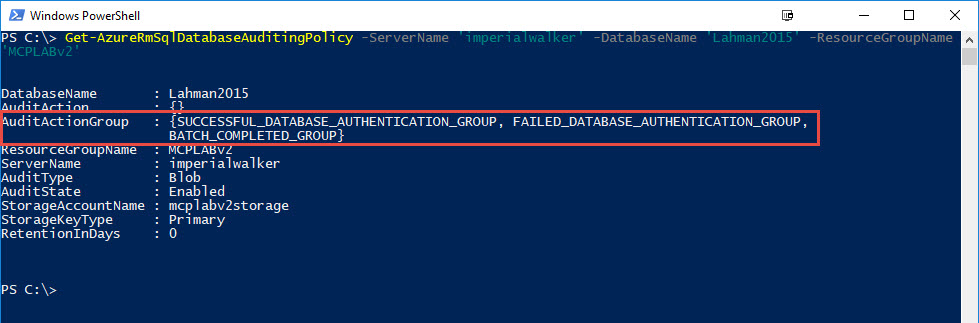
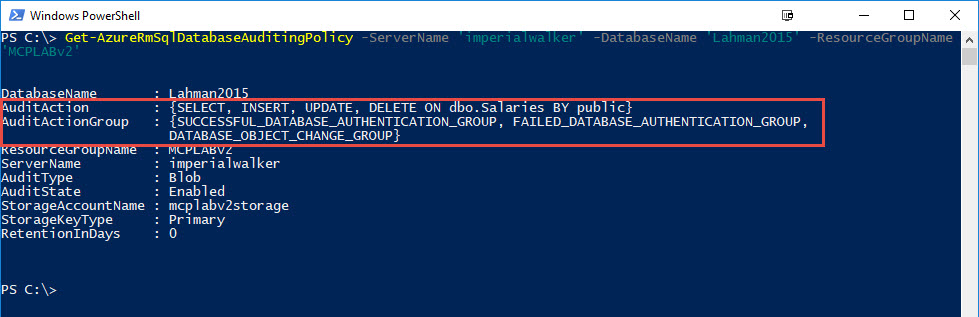
Using PowerShell, we can easily see the default audit action groups.
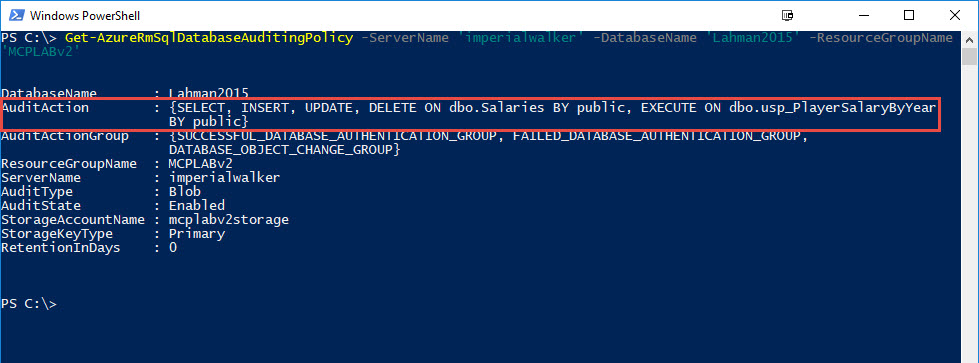
Get-AzureRmSqlDatabaseAuditingPolicy ` -ServerName 'imperialwalker' ` -DatabaseName 'Lahman2015' ` -ResourceGroupName 'MCPLABv2'
We can see there are three action groups listed: SUCCESSFUL_DATABASE_AUTHENTICATION_GROUP, FAILED_DATABASE_AUTHENTICATION_GROUP, and BATCH_COMPLETED_GROUP. Without even looking at the documentation, we can assume that we are auditing both successful and failed logins, as well as all successful batches against this database. When you compare the Azure action groups side-by-side with the box product, they line up almost exactly.
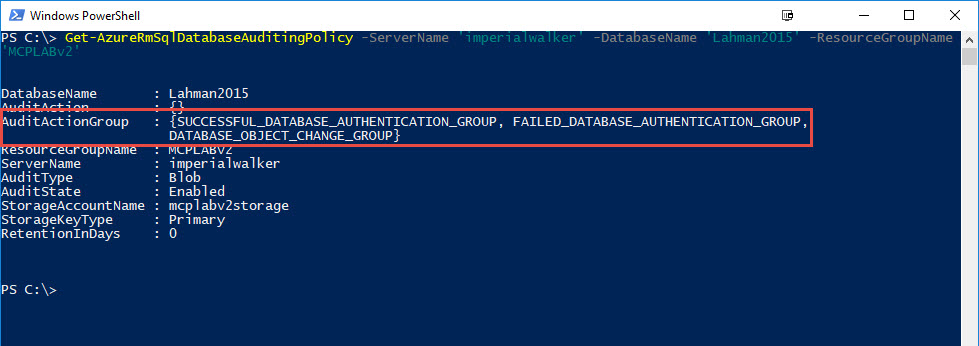
So how do we customize it further? Well let’s say our auditing requirements only need to capture changes to structure of the database; for example, an ALTER TABLE. First, we need to remove BATCH_COMPLETED_GROUP and add DATABASE_OBJECT_CHANGE_GROUP. To accomplish this, we will use Set-AzureRmSqlDatabaseAuditingPolicy.
Set-AzureRmSqlDatabaseAuditingPolicy `
-ServerName 'imperialwalker' `
-DatabaseName 'Lahman2015' `
-ResourceGroupName 'MCPLABv2' `
-AuditActionGroup `
'SUCCESSFUL_DATABASE_AUTHENTICATION_GROUP' `
,'FAILED_DATABASE_AUTHENTICATION_GROUP' `
,'DATABASE_OBJECT_CHANGE_GROUP'
To verify the changes were successful, we run Get-AzureRmSqlDatabaseAuditingPolicy again.
Now, we’ll be able to collect audit records anytime a CREATE, ALTER, or DROP is executed against a database object. However, let’s say we need something more granular. In our sample database, we have a table that stores salary data and we need to audit anything that touches it. We ae already covered with schema changes by the action group, DATABASE_OBJECT_CHANGE_GROUP, but that doesn’t audit DML changes. Adding BATCH_COMPLETED_GROUP would capture what we need, but that would cover all tables and we have a requirement for just one. This is where we can audit actions on specific objects. In the statement below, we just add an audit action for SELECT, INSERT, UPDATE, and DELETE on the Salaries table.
Set-AzureRmSqlDatabaseAuditingPolicy `
-ServerName 'imperialwalker' `
-DatabaseName 'Lahman2015' `
-ResourceGroupName 'MCPLABv2' `
-AuditActionGroup `
'SUCCESSFUL_DATABASE_AUTHENTICATION_GROUP' `
,'FAILED_DATABASE_AUTHENTICATION_GROUP' `
,'DATABASE_OBJECT_CHANGE_GROUP' `
-AuditAction 'SELECT, INSERT, UPDATE, DELETE ON dbo.Salaries BY public'
To verify the changes were successful, we run Get-AzureRmSqlDatabaseAuditingPolicy again.
If you have multiple objects or actions to audit, then just separate them with a comma, just like the AuditActionGroups parameter. The one key piece to remember is you must specify all audit actions and action groups together with each execution of Set-AzureRmSqlDatabaseAuditingPolicy. There is no add or remove audit item. This means if you have 24 actions to audit and you need to add one more, then you have to specify all 25 in the same command.
Now let’s run a few queries to test the audit. First, we’ll run a simple select from the Salaries table.
SELECT TOP 10 * FROM dbo.Salaries; GO
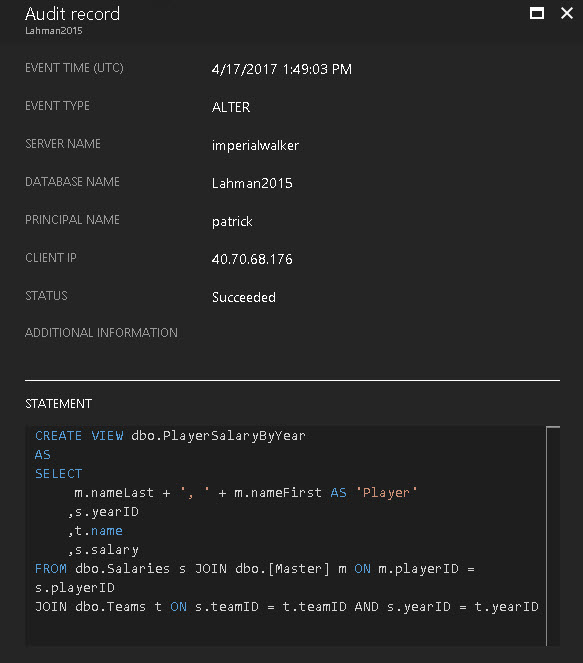
Next, we’ll create a view that selects from the Salaries table.
DROP VIEW IF EXISTS dbo.PlayerSalaryByYear; GO CREATE VIEW dbo.PlayerSalaryByYear AS SELECT m.nameLast + ', ' + m.nameFirst AS 'Player' ,s.yearID ,t.name ,s.salary FROM dbo.Salaries s JOIN dbo.[Master] m ON m.playerID = s.playerID JOIN dbo.Teams t ON s.teamID = t.teamID AND s.yearID = t.yearID; GO
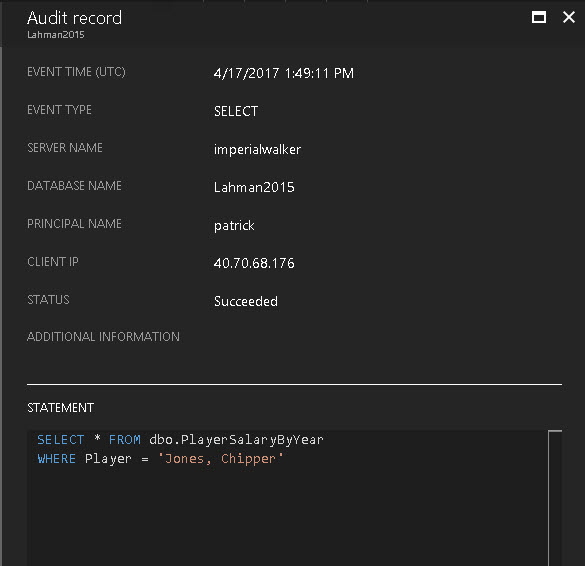
Finally, we’ll select from that view.
SELECT * FROM dbo.PlayerSalaryByYear WHERE Player = 'Jones, Chipper'; GO
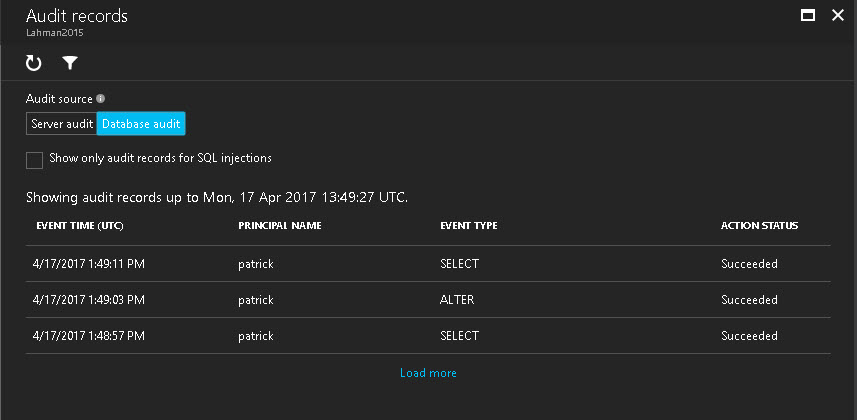
Back in the Azure Portal, click on the view button so we can view the captured audit records for the statements we just executed.
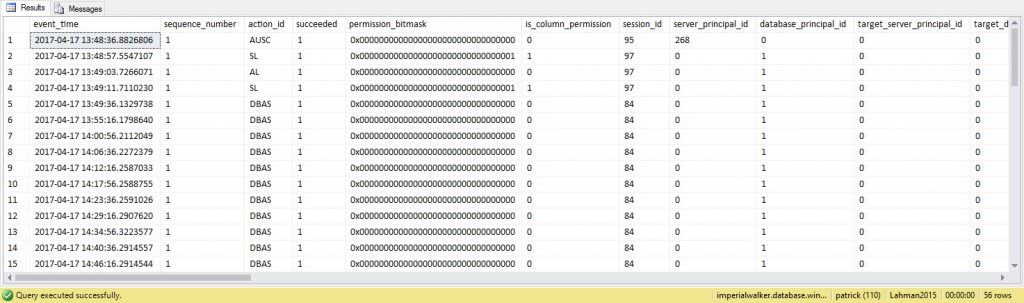
What is displayed is one line item for each audit record captured.
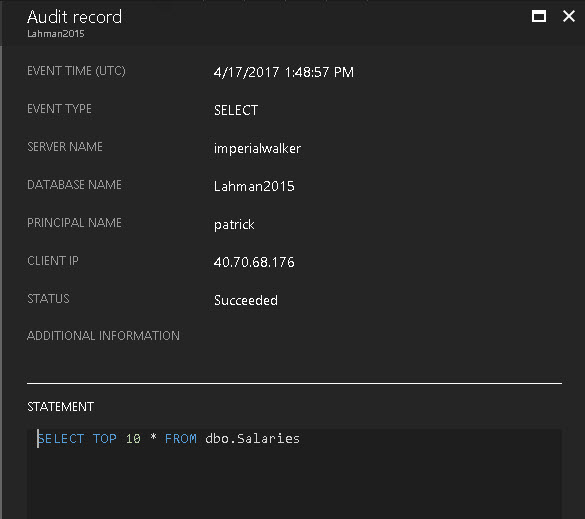
Selecting each record will open another blade with the contents of that record. In our example, we have one for the initial SELECT against the table, one for the CREATE VIEW statement, and one for the SELECT against the view which references the Salaries table.
While using the Azure Portal is a quick and easy way to view audit records, the best way to consume the records for reporting is to use the function, sys.fn_get_audit_file(). This is the same function used in the box product. The only difference is we need to specify the Azure URL for the audit log. All audit logs are stored in a container named sqldbauditlogs. In side that container, additional containers server name, database name, and a date/time stamp are created to further organize it. This is something to keep in mind if you plan to programmatically process the audit records.
SELECT *
FROM sys.fn_get_audit_file ('https://mcplabv2storage.blob.core.windows.net/sqldbauditlogs/imperialwalker/Lahman2015/SqlDbAuditing_Audit_NoRetention/2017-04-17/13_48_34_960_0.xel',default,default);
GO
If you don’t know the URL full path, you can use the Azure Storage Explorer to help find it.
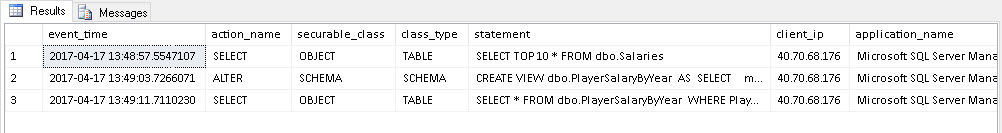
As of this writing, there are two DMVs missing from Azure SQL Database: sys.dm_audit_actions and sys.dm_audit_class_type_map. These DMVs allow us to translate the actions_id and class_type values into a readable description. Since they are not available in Azure, I have created my own version of those as user tables within my database: dbo.audit_actions and dbo.audit_class_types. This allows me to join them against the audit function to produce a better report.
SELECT
a.event_time
,aa.name AS 'action_name'
,c.securable_class_desc AS 'securable_class'
,c.class_type_desc AS 'class_type'
,a.statement
,a.client_ip
,a.application_name
FROM sys.fn_get_audit_file ('https://mcplabv2storage.blob.core.windows.net/sqldbauditlogs/imperialwalker/Lahman2015/SqlDbAuditing_Audit_NoRetention/2017-04-17/13_48_34_960_0.xel',default,default) a
LEFT JOIN dbo.audit_actions aa ON a.action_id = aa.action_id
LEFT JOIN dbo.audit_class_types c ON a.class_type = c.class_type;
GO
If you are familiar with auditing in the box product, then you might be aware that common properties like client hostnames (or IP address) and application names are not captured for each audit record; however, in Azure they are collected and viewable in the columns client_ip and application_name. See the picture above.
Next, let’s create a stored procedure that selects from that view and add an EXECUTE audit action for it.
DROP PROCEDURE IF EXISTS dbo.usp_PlayerSalaryByYear; GO CREATE PROCEDURE dbo.usp_PlayerSalaryByYear(@playerName varchar(100)) AS SELECT * FROM dbo.PlayerSalaryByYear WHERE Player = @playerName; GO
Now to add the EXECUTE audit action via PowerShell.
Set-AzureRmSqlDatabaseAuditingPolicy `
-ServerName 'imperialwalker' `
-DatabaseName 'Lahman2015' `
-ResourceGroupName 'MCPLABv2' `
-AuditActionGroup `
'SUCCESSFUL_DATABASE_AUTHENTICATION_GROUP' `
,'FAILED_DATABASE_AUTHENTICATION_GROUP' `
,'DATABASE_OBJECT_CHANGE_GROUP' `
-AuditAction `
'SELECT, INSERT, UPDATE, DELETE ON dbo.Salaries BY public' `
,'EXECUTE ON dbo.usp_PlayerSalaryByYear BY public'
Using Get-AzureRmSqlDatabaseAuditingPolicy, you can see the additional audit action that was added.
Now we need to execute the stored procedure to test.
EXECUTE dbo.usp_PlayerSalaryByYear 'McGriff, Fred'; GO
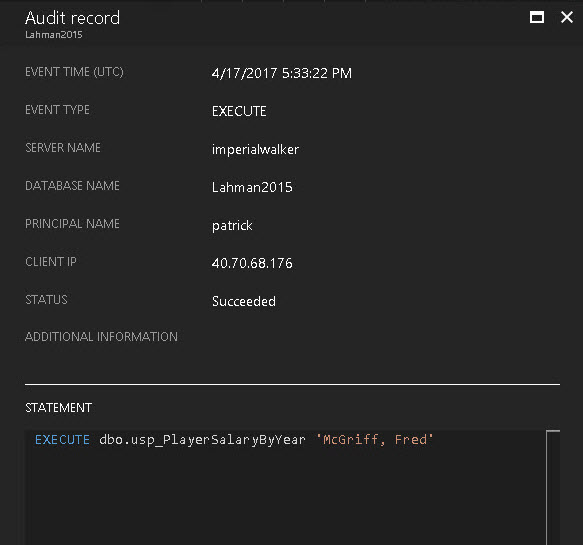
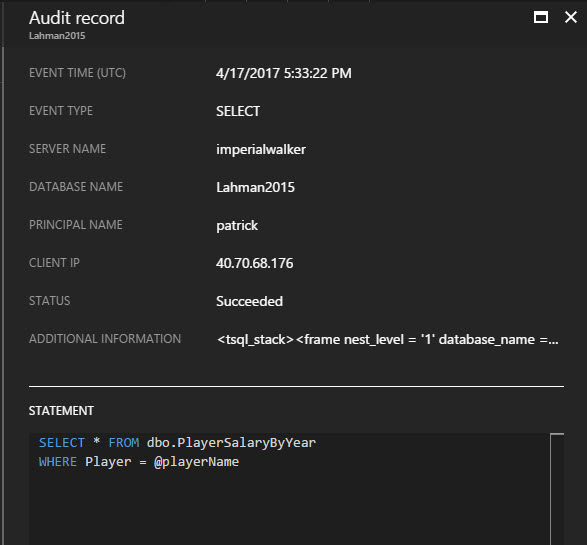
The Azure Portal shows the two audit records that were captured; one for the execute of the stored procedure and the second for the select on the underlying table.
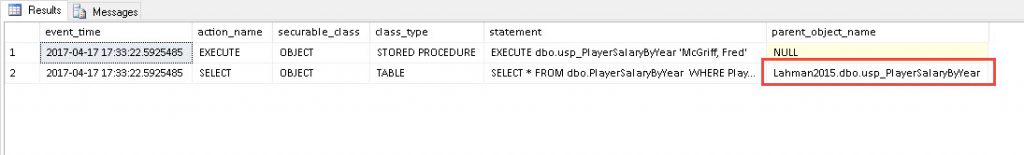
Using the query below, we can extract some more useful data from the additional_information column. This will show the nested objects and we’ll be able to extract the parent object name.
SELECT
a.event_time
,aa.name AS 'action_name'
,c.securable_class_desc AS 'securable_class'
,c.class_type_desc AS 'class_type'
,a.statement
,CONVERT(XML,a.additional_information).value('(/tsql_stack/frame/@database_name)[1]','varchar(100)')
+ '.' + CONVERT(XML,a.additional_information).value('(/tsql_stack/frame/@schema_name)[1]','varchar(100)')
+ '.' + CONVERT(XML,a.additional_information).value('(/tsql_stack/frame/@object_name)[1]','varchar(100)') AS parent_object_name
FROM sys.fn_get_audit_file ('https://mcplabv2storage.blob.core.windows.net/sqldbauditlogs/imperialwalker/Lahman2015/SqlDbAuditing_Audit_NoRetention/2017-04-17/17_32_29_811_0.xel',default,default) a
LEFT JOIN dbo.audit_actions aa ON a.action_id = aa.action_id
LEFT JOIN dbo.audit_class_types c ON a.class_type = c.class_type;
GO
As you can see, Blob Auditing for Azure SQL Database provides us with major improvements over Table Auditing, and gives us the flexibility and granular control that we are used to in the box product.
For more information on the auditing features for Azure SQL Database, follow these links.
https://docs.microsoft.com/en-us/azure/sql-database/sql-database-auditing
https://docs.microsoft.com/en-us/powershell/module/azurerm.sql/set-azurermsqldatabaseauditingpolicy
https://msdn.microsoft.com/library/azure/mt695939.aspx

Whatever I do sys.fn_get_audit_file return nothing! No error, nothing. Even if I pass a wrong filename it is the same story!
Could you please elaborate on the file path value more
The only issue I can think of is a permission issue. Have you attempted to download the audit file to read it using a local file path?
https://docs.microsoft.com/en-us/sql/relational-databases/system-functions/sys-fn-get-audit-file-transact-sql?view=sql-server-2017#examples